Business Security: How Safe Is Your Office?
May 10, 2012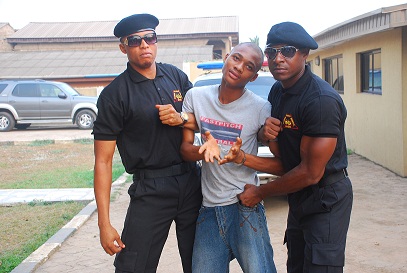
School Security: How Safe Is The Nigerian Learning Environment?
June 29, 2012So many people experience a loss of some kind or another throughout their life – and it is almost always unfortunate. While the frustration and experiences are inevitable, there are varying forms of security measures in place to alleviate certain portions of the experience.
In previous articles, we’ve looked at different forms of ensuring the safety of your life and properties, some of which include; Manned Guarding, Security Dogs, Executive protection, home security and business security.
These are just a few out of several other forms of security measures available for private and public safety depending on the nature of threat at stake. For example, the provision of security also involves the use of technology. This is a form of security known as security systems. This is going to be the focus of this article.
What Is Security Systems?
An electronic system that is designed to prevent theft or intrusion and protect property and life. There are a wide variety of security systems available to every person and business today.
Examples include;
- Car security systems,
- Home security systems,
- Video surveillance security systems,
- Identity security systems,
- Computer security systems
- Access control systems,
- Burglar alarm systems,
- Fire alarm systems,
- Etc.
There are also different types of each security system:
- Wireless
- Hardwired
- Digital
- Analog
- Motion Sensors
- Acoustic Sensors
- etc.
4 Ways Of Using Security Systems For Personal And Business Protection
- For Your Home
Home security systems are used by homeowners to make sure their homes are well-protected from theft, burglars, fires and other disasters. Many people decide which type of home security system to purchase depending upon the neighborhood in which they live, how much security they want and how much they are willing to pay for the security.
The types of home security systems available for installation fall under two categories;
- Unmonitored – the unmonitored home security system is the most popular and cost-effective system on the market today. When the alarm is triggered by a burglar, it produces a loud siren noise on the inside and outside of the home. A majority of the time the siren will scare off the intruder before he even enters the home. If you aren’t at home when the alarm is tripped, it will be up to your neighbors to call the police, as this type of system doesn’t contact the monitoring company for you.
- Monitored – the monitored home security systems are ones that alert the monitoring company when the system is tripped by a burglar or intruder. Monitored systems also signal the authorities in the event of a fire, gas leak and flood. The biggest advantage to this type of system is you don’t have to depend on your neighbors to be home to contact the authorities for you.
2. For Your Business
What home security systems do for homes, business security systems do for businesses. It doesn’t matter if you run a small business or operate a large company; you need to take certain safety precautions to ensure the safety of it, as well as any employees who may be working there too. Business security systems are highly effective at not only keeping burglars out, but they are also an effective way to deter internal theft as well. The first step to design the best security system for your business is to sit down with a security company and discuss the nature of your business operations.
There are three basic types of business security systems available.
- Video Surveillance System (or CCTV) – This is the most common type of security system for a company that wants to monitor employee activity. In general, businesses will point the camera toward cash registers or safes and then hook up the video in a secure office. This allows a boss to watch over employees at all times. This is most popular if you run a company that operates overnight.
- Access Control – These systems work very much like most home security systems. This requires employees to punch in a code on a keypad or swipe a card in order to get into the building. This isn’t quite as fancy as a video surveillance system, but it works great if you want to keep unauthorized people out of the building. These systems generally don’t have a video, but an alarm will sound when someone breaks in the building or office without knowing the code or having a keycard. Many access control systems will even wait 30 seconds and then alert authorities.
The three primary functions of access control security systems are;
- To monitor the locations of individuals within a building,
- Control where individuals are able to gain access and
- Manage individual user permissions to ensure that access is granted to the correct individual to the correct areas at the correct times.
- Wireless – Wireless systems are usually used by companies expecting to move offices. There are no wires to deal with and the systems are mobile. However, it is the responsibility of the business owner to change batteries and call the police if there is any suspicious activity.
3. For Your Car
Our cars and automobiles are almost always easier targets for criminal intent than our homes, businesses or identities. We take our cars everywhere – and we park in parking garages, driveways, street-side and parking lots, all of these areas usually have limited visibility at night or they make for an easy target for theft during the day. A car security system is designed to help curb theft and unauthorized entry.
There are three basic types of car security systems available.
- Audible car security system – is one which, when set off, lets anyone within range of the protected car or truck know that there is an active theft deterrent device in place for the vehicle. The alert this car security system provides is a very loud noise. Some audible systems have a computerized voice that commands the potential thief to get back away from the vehicle. Others trigger the horn of the car to honk and many have whistling or similar sounding alarms. Many are very sensitive to movement near or around the vehicle but the sensitivity can be adjusted to different levels.
- Inaudible car security system – is one that is unheard by whoever or whatever activated the alarm. An alert is sent to the vehicle owner’s mobile phone via a SMS or other message device programmed to the security system. Be aware though, that this type of car security system does not warn the intruder so by the time you get to your vehicle, it may have already been damaged, the contents stolen, or worse yet your car stolen.
- Computerized car security system – is one that is controlled by a computerized program in which the system has to be stalled before the vehicle can be started. It prevents the probability of your car being started without authorization from the program by use of a specially coded or numerical entry designed for that specific car security system. Overall, this is most likely the most reliable theft deterrent system compared to the others that are available.
Although car security systems are effective to a degree, none of them are fool proof if a thief really wants to steal your car. The degree of security you get from a system depends largely upon the type of system you choose.
4. For Your Information
Information security means protecting information and information systems from unauthorized access, use, disclosure, disruption, modification, perusal, inspection, recording or destruction. Information security is concerned with the confidentiality, integrity and availability of data regardless of the form the data may take: electronic, print, or other forms.
There are two basic types of information security systems available.
- Computer Security – most personal computers come with limited to no virus protection. A virus can delete all of your timeless photographs, send all of your user names and passwords to a thief, and render your computer useless. All of these can cost you stress, time and a lot of money and frustration. There are a lot of virus and internet protection software available on the market today.
- Identity Theft & Credit Card Security — did you know that most people do not have credit or identity protection? Your identity and credit are at risk daily through using computers, cell phones, ATM machines and more. We don’t want to scare you, but big companies lose millions of pieces of information regularly – what happens if it happens to you? It’s time to think about protecting your identity and your credit.
Your Turn
For the implementation of any of the above listed security systems, contact us today for a professional consultation.




297 Comments
Wow, thanks. Here is a nice information. Well done.
Thanks Daniel for the nice words. Glad you found the article useful.
One of the key areas that people overlook in their CCTV system design is getting an identification image in at least one location.
This is a common reason why much of the surveillance footage is useless. It gives an overview of movement, which is needed but you also need to ID the person, typically as the enter or leave the site.
Tim,
Thank you for stopping by and dropping this additional info on how to get the most from CCTV.
[…] estate security or residential security guards, having a guard dog, installation of CCTV, using technology, and as simple as locking every entry and exit points at home and at […]
This is really a great article. Pls keep them coming.
Heya just wanted to give you a brief heads up and
let you know a few of the pictures aren’t loading properly. I’m
not sure why but I think its a linking issue. I’ve tried it in two different web browsers and both show the same results.
I found this article very useful, technology can be very useful to protect our businesses and especially our precious home. Try to refresh your page twice and you will see the photo in your browser.
I’m impressed, I must say. Seldom do I encounter a blog that’s equally educative and entertaining, and without a
doubt, you’ve hit the nail on the head. The problem is an issue that too few people are speaking intelligently about. I’m very happy I
stumbled across this during my hunt for
something regarding this.
I usually do not drop a ton of comments, but i did some searching and wound up here Security Systems 101: How To Use Technology For Your Personal And Business Protection | Threat Alert!
– by Damog Guards. And I do have a couple of questions for you if it’s allright. Could it be simply me or does it look as if like some of these responses come across as if they are coming from brain dead people? 😛 And, if you are writing at additional online sites, I’d like to follow everything
fresh you have to post. Would you make a list of
every one of all your public sites like your linkedin profile,
Facebook page or twitter feed?
Fantastic submit, very informative. I wonder why the other specialists of this sector do not notice this. You must continue your writing. I am confident, you have a huge readers’ base already!|What’s Taking place i’m new to this, I stumbled upon this I have found It positively useful and it has aided me out loads. I’m hoping to give a contribution & help other customers like its helped me. Great job.
I got this web site from my buddy who shared with me on the topic of this site and now this time I am browsing this
web page and reading very informative posts
at this time.
I’m very pleased to find this page. I wanted to thank you for ones time for this particularly fantastic read!! I definitely enjoyed every part of it and I have you saved as a favorite to look at new stuff in your website.
Hi there! I’m at work browsing your blog from my new iphone 4! Just wanted to say I love reading through your blog and look forward to all your posts! Carry on the superb work!
I am sure this piece of writing has touched all the internet people, its really really pleasant piece of writing on building up new
website.
Thank you a bunch for sharing this with all people you really understand what
you’re talking about! Bookmarked. Please additionally consult with my site =). We could have a link alternate contract among us
General public tastes these days control the entertainment market place in a manner which has beennot possible prior to the the web along with the virus-like delivery of media, and even entire entertainment material. Should you add to that distribution on the web and, press, sites, from chat to complete videos. It’s a really totally new environment. Some of it very good, some not.
Very fantastic post. I recently became aware of your website plus wanted to state that I definitely liked exploring your blog blogposts. All things considered I’ll be opting-in for the rss feed using this program . intending you’re writing yet again immediately!
added internet site cannote not unblocked after erase the line
This is a very enlightening post. With the increasing crime rate,home invasion remains a serious threat. Unguarded and guarded homes and offices are burgled with impunity.
We are introducing our product, the Intelligent Guard System, to virtually eliminate burglary, incursion and vandalizing of our homes and offices whether we are in or away.GSM wireless security alarm system is a self-monitoring alarm system that allows the user to keep an eye on his/her property and business wherever he/she is.If an intrusion, fire out break or any other problem identified by one of the sensors occurs, the system can automatically dial and send text messages (SMS) to mobile phone numbers, stating the alarm types, alarm time and zone number information, this allows the user to know the alarm activation reason and exactly which zone was triggered and address where the intrusion has taken place.
Follow us on twitter @Drukas3 or email andrewogodo@yahoo.com for more information.
88888 We are not sure should they be more than enough to stop a pedicab driver, but we have not yet positioned a lot of of our self worth of their palms.. Internet TutorialsLet’s experience it, quite a few of us don’t provide the time or cash make use of hair dressers, louis vuitton speedy 40 price makeup artists and stylists on even an occasional foundation.
Cheap Louis Vuitton Bags Online Outlet http://www.nicelouisvuittonbags.com/
You actually make it seem so easy with your presentation but I find this matter to be actually
something that I think I would never understand.
It seems too complex and extremely broad for me.
I am looking forward for your next post, I’ll try to get the hang of it!
Normally I don’t read article on blogs, however I wish to say
that this write-up very compelled me to take a look at and do it!
Your writing taste has been surprised me. Thanks,
quite nice article.
Howdy! I know this is kind of off topic but I was wondering which blog platform are you using for tis site?
I’m getting sick and tired oof WordPress because I’ve had
problems with hackers and I’mlooking at options for another platform.
I would be great if you could point me iin the direction of a good
platform.
Pretty nice post. I just stumbled upon your blog and wished to say that I’ve really enjoyed browsing your blog posts.
In any case I will be subscribing to your feed and I hope you
write again very soon!
Hey I know this is off topic but I was wondering if you knew of any widgets
I could add to my blog that automatically tweet my newest twitter updates.
I’ve been looking for a plug-in like this for quite some time and was hoping maybe you would have some
experience with something like this. Please let me know if you run into anything.
I truly enjoy reading your blog and I look forward to your new updates.
Spot on with this write-up, I honestly think this website needs a lot more attention.
I’ll probably be back again to read more, thanks for the
advice!
my blog post – telecharger pdf creator
A comprehensive look at different security solutions for various scenarios and their pros & cons.
I believe this is one of the such a lot significant information for me.
And i’m happy reading your article. But wanna commentary on few basic things, The website style is ideal, the articles
is actually great : D. Good activity, cheers
This is a topic that’s near to my heart… Take care!
Exactly where are your contact details though?
After looking over a number of the blog posts on your site, I really appreciate
your technique of blogging. I book marked it to my bookmark
webpage list and will be checking back soon. Take a look at my web site too and tell me how you feel.
In fact when someone doesn’t be aware of then its up to other visitors that
they will assist, so here it occurs.
Lets use wi-fi, alram, video and also best home security camera system to safe gaurd our valuable.
Power back-up feature is another important one that should not be ignored while choosing the perfect home alarm system. It is important as it helps the alarm system work properly even during the power cuts.
<a href="" title="http://www.besthomesecuritycamerasystem.com/"<Best home alarm system,
Great article! Thanks for sharing
Good post! I found this post helpful as Im looking for ways of intensive security at home. With a wide variety of security systems, it’s confusing, but not at all after I read your post.
At All Safe Security, our mission is to ensure that your home or business is always safe and secure with the use of higher Security services at very honorable price.
It’s remarkable in support of me to have a site, which is valuable designed for my know-how.
thanks admin
Hi blogger, i found this post on 17 spot in google’s search results.
I’m sure that your low rankings are caused by hi bounce rate.
This is very important ranking factor. One of the biggest reason for high bounce rate is
due to visitors hitting the back button. The higher your bounce rate the further down the search results your posts and pages will end up, so having reasonably low
bounce rate is important for improving your rankings naturally.
There is very useful wp plugin which can help you. Just search in google for:
Seyiny’s Bounce Plugin
Nice composition.I like the way how you deliver the importance and a few considerations of having a security system at home and at a business area.You’re definitely right saying that the security level also depends on the type of security tool to choose.
Security systems and our security or provide protection to our house and our family
I personally have an unmonitored system. I do like that even though it is unmonitored the camera still work. You will need to know how to program these things, but it is pretty simple and the internet will help you. http://security-unlimited.com/convention-services/
I am starting up my own business this year. Almost everything is planned. However, the biggest obstacle right now is protecting my actual business office. We’ll have product supplies that need to be secured overnight. For that reason, I want to have a great alarm system installed.
Hi Kemi, thanks for the article. I have been looking for a car security system. I wanted to learn more about the computerized car security system, and I did! Thanks again.
Well done such a great blog, very informative. With this explanation you can identify the differences.
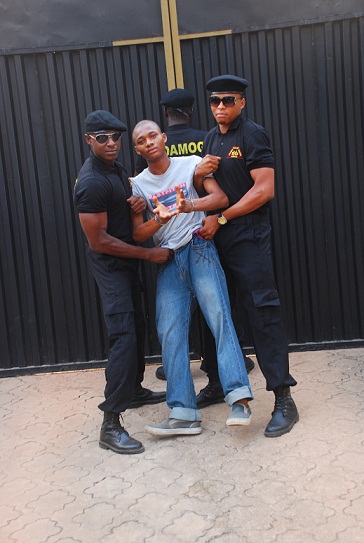
Hey there. This is absolutely outstanding information. I really like the pictures and the shirts. Very cool stuff. Thanks.
esync security is the reputed cctv distributors in chennai Offer best services http://securehome.in/ had done cctv camera manufacturers, cctv camera suppliers, cctv camera exporters,closed circuit Television camera,closed circuit television cam production centers. To know cctv distributors in chennai call us 7299004295.
This is wonderful stuff. Brilliant news. Great picture 🙂
[…] Security Systems 101: How To Use … – Security Systems 101: The provision of security also involves the use of technology. Here are 4 Ways To Use Technology For Your Personal And Business […]
Excellent article. I’m dealing with a few of these issues as well..
Great Share!!
Such type of technical information is genuinely required these days and above all to be shared with everyone around us to make them aware that by making small efforts, they can stop unexpected and bigger mishaps and accidents.
Digital security systems are easily available these days. We just have to chosoe the right one according to our need and requirment.
Thank you for sharing this rmative post with us.
Given details everything very nice for blog readers. I really want to agree with you and extremely thank for this blog. Most websites designed for sharing knowledge and announcement to others. Security Devices have been secure your valuable property from unknown accesses. Example: Surveillance camera, Alarm Systems and Automation systems for home and Work Locations. How? Visit: http://securehome.in
Absolutely awesome post I was having trouble with thinking about topics for my search niche. Thanks for giving very good informations. Really given details everything is very easy to understand and followable ways. beginners always support this page informations. keep your good thinks update here.. I want to get more knowledge from here…thanks by kumar
Hi!You composed an interesting piece about security systems. I find your page readable and informative. Keep on posting!
Call me up for the Technical installations of all your security systems installations.
0805 187 0955
Always is a great choice having a good security system.
Absolutely awesome post I was having trouble with thinking about topics for my search niche. Thanks for giving very good informations. Really given details everything is very easy to understand and followable ways. beginners always support this page informations. keep your good thinks update here.. I want to get more knowledge from here…thanks by kumar
I prefer the monitored security system. It is ideal for frequent travelers like me.This gives me so much security even when I’m not home.
Hi Kemi,
Such a great and well explained post by you. Your post contains all the information which may be helpful for everyone, whether they are like-homeowner, car owner & businessman. You covered each topic of security system. Thanks for sharing and waiting for next update!!!!!
Surveillance cameras can be accessed remotely on our computers, smartphones, or tablets. These cameras often used when homeowner is out of town.
So it gives us the ability to see with our own eyes that everything is alright at our homes.
CCTV in different places in your establishment acts as a monitor and allows you access to any unprofessional behaviour at work. Security measures such as CCTV cameras, recorders, and fingerprint protected access control systems ensure legal help if things go wrong. CCTV recording maybe entered as evidence with the police and often helps them track down miscreants.
Nowadays, technology is playing a important roll in our security concerns. It is very essential to keep our home,business & vehicles safe. Your post is so impressive & direct relate to safety.
Thank you for posting this blog…..
It’s good to know that a monitored system also signals if there is a fire. It’s important that your home or business is protected while you are away so finding a system that also works for fires is a great way to do that. It would Testing the equipment regularly would be a good way to ensure it will work when it needs to.
Thanks for the post buddy. We recently had a home security system installed (a monitored home security system, by the way) and every time we leave the house we laugh and remember the episode of ‘My Family’ when the Harper family gets a monitored home security system installed (if you haven’t seen it you should.. I’m sure you’d find it funny given the context!) Thanks again for posting about security systems!
In general, businesses will point the camera toward cash registers or safes and then hook up the video in a secure office.
cialis for daily use side effects
Мадонна, икона поп-музыки и культурного влияния, продолжает вдохновлять и поражать своей музыкой и стилем. Её карьера олицетворяет смелость, инновации и постоянное стремление к самовыражению. Среди её лучших песен можно выделить “Like a Prayer”, “Vogue”, “Material Girl”, “Into the Groove” и “Hung Up”. Эти треки не только доминировали на музыкальных чартах, но и оставили неизгладимый след в культурной и исторической панораме музыки. Мадонна не только певица, но и икона стиля, актриса и предприниматель, чье влияние простирается далеко за рамки музыкальной индустрии. Скачать mp3 музыку 2024 года и слушать онлайн бесплатно.
Excellent write-up
how does furosemide work
http://vrn.best-city.ru/forum/thread540106536/
hctz/lisinopril
flagyl and diflucan
zoloft sleepy
lasix alternative
gabapentin brand name
zithromax pediatric dose
glucophage cholesterol
how much gabapentin can i give my cat
cephalexin same as keflex
http://igre.listbb.ru/viewtopic.php?f=11&t=1831
https://ecokom.ru/forum/viewtopic.php?f=5&t=7631
escitalopram buy
http://domovou.3nx.ru/viewtopic.php?p=4241#4241
https://womens-forum.ru/viewtopic.php?f=59&t=5478&sid=d8207d386c183d20d614bcb089df0a5d
http://bondpedia.altervista.org/index.php?title=Utente:CDRAli20388
https://dokuwiki.stream/wiki/Mp3bit.pw_3
https://kozaostra.mybb.ru/viewtopic.php?id=11591#p94803
antibiotics amoxicillin
http://g29869x8.beget.tech/2024/01/20/istoriya-audioformatov-ot-vinila-do-striminga.html
https://samaramed.ru/forum/health/topic_39949.html
http://kissolovo.teamforum.ru/viewtopic.php?f=10&t=31972
https://gefi.io/index.php?title=User:HiramLongwell0
https://finansforum.apbb.ru/viewtopic.php?id=11064#p148483
http://boxer-forum.ru/viewtopic.php?f=24&t=3107
http://x-universe.ru/index.php?title=%D0%AD%D0%B2%D0%BE%D0%BB%D1%8E%D1%86%D0%B8%D1%8F_%D0%97%D0%B2%D1%83%D0%BA%D0%B0:_%D0%9F%D0%BE%D0%BF%D1%83%D0%BB%D1%8F%D1%80%D0%BD%D1%8B%D0%B5_%D0%9C%D1%83%D0%B7%D1%8B%D0%BA%D0%B0%D0%BB%D1%8C%D0%BD%D1%8B%D0%B5_%D0%90%D0%BB%D1%8C%D0%B1%D0%BE%D0%BC%D1%8B_%D0%A1_%D0%9D%D0%B0%D1%87%D0%B0%D0%BB%D0%B0_90-%D1%85
does bactrim cause headaches
http://cinemania.forum24.ru/?1-15-0-00000794-000-0-0-1706616226
https://philosophie-en-cours.net/liaisons/index.php?title=Mp3gid.co
https://spshn.ru/plugins/forum/forum_viewtopic.php?344289.-0#post_344289
cephalexin interactions
http://swwwwiki.coresv.net/index.php?title=%E5%88%A9%E7%94%A8%E8%80%85:DamienCurtain30
http://site2.liodiz.ru/2024/02/01/filosofiya-i-teksty-hip-hop-pesen.html
https://zarabotok.forumrpg.ru/viewtopic.php?id=68926#p150024
para que es ciprofloxacin
http://morrowindsv.2bb.ru/viewtopic.php?id=908#p2862
http://31pokupki.rx22.ru/viewtopic.php?f=47&t=24988
http://gb3nq.co.uk/wiki/index.php?title=Mp3gid.co
http://www.springst.melbourne/index.php/Mp3bit.pw_2
https://happygirls.webtalk.ru/viewtopic.php?id=317#p928
http://webjob.spybb.ru/viewtopic.php?id=3022#p6171
http://oksano4ka1.nnov.org/blog/dzhaz__ritmy_svobody_i_improvizatsii.html
https://remontmix.ru/forum/viewtopic.php?t=8035
https://telearchaeology.org/TAWiki/index.php/User:RickieCollits6
uti bactrim dose
cephalexin ear infection
gabapentin dosage for chronic pain
can you snort escitalopram
citalopram over the counter
ddavp urine output
valproic acid depakote
cozaar alternatives
citalopram hbr 40 mg
what does depakote treat
dose ddavp
ezetimibe clinical evidence
side effects of diltiazem 120 mg
prozac vs effexor
taking contrave at night
Привет. С радостью делимся информацией о релизе улучшенного мобильного приложения букмекерской Олимп! Скачать Олимп бет на андроид уже сегодня! Приложение стало более удобнее и быстрее, предоставляя доступ к широкому спектру ставок на спорт с телефонов. С новейшим обновлением вы получаете расширенные функции управления вашим счетом, обновленный дизайн для более интуитивного пользования, а также улучшенную скорость работы. Подключайтесь к довольным пользователям и совершайте свои ставки с удовольствием и комфортом в любое время и в любом месте. Загрузите актуальную версию приложения букмекерской конторы сегодня и играйте вместе с Олимп!
what is the mechanism of action of allopurinol (zyloprim)?
Восторгаемся возможностью анонсировать новейшее обновление приложения от БК Олимп для Android! Ваше умение и опыт со ставками на спорт теперь станет невероятно комфортным благодаря усовершенствованному интерфейсу и оптимизированной работе программы. Olimp bet на телефон уже сегодня! С последней версией приложения вы получите неограниченный доступ к разнообразию спортивных событий прямо с вашего мобильного устройства. Ожидайте расширенные возможности для управления счетом, передовой дизайн для интуитивного пользования и значительное улучшение скорости приложения. Станьте частью довольных клиентов БК Олимп и радуйтесь ставкам где угодно и когда угодно. Установите последнюю версию приложения без промедления и начните выигрывать вместе с Олимп!
С энтузиазмом объявляем о запуске нового мобильного приложения БК Олимп для Android устройств! Этот релиз значительно улучшает ваше прежнее взаимодействие с ставками, делая его проще и эффективным. Скачать апк файл Олимп Бет доступное для игроков! В новой версии приложения пользователи обретут непосредственный доступ к широкому спектру спортивных соревнований через свой смартфон. Оптимизированное управление аккаунтом, передовой дизайн для легкого навигации и значительное ускорение работы приложения – всё это ждет вас. Станьте одним из удовлетворенных пользователей и испытывайте радость от ставок где угодно и в любой момент. Загрузите обновление приложения БК Олимп сегодня и откройте для себя новый уровень ставок!
aripiprazole dosage forms
С огромной радостью делимся новостью о релизе обновленной версии мобильного приложения от БК Олимп для Android! Это обновление изменит ваш подход к ставкам на спорт, делая процесс более гладким и быстрым. Скачать Olimp на андроид и вы получите легкий доступ к широкому ассортименту спортивных мероприятий, открытых для ставок прямо с вашего мобильного. Усовершенствованные функции управления профилем, интуитивный дизайн для упрощения навигации и значительное повышение скорости приложения обещают выдающийся опыт. Присоединяйтесь к сообществу энтузиастичных клиентов и наслаждайтесь ставками в любом месте, когда захотите. Установите последнюю версию приложения БК Олимп уже сейчас и выходите на новый уровень ставок с комфортом и стилем!
will aspirin lower blood pressure before physical
Энергично разглашаем новостью о выпуске новаторской версии приложения для ставок от БК Олимп на Android! Это обновление преобразует ваш подход к ставкам, делая процесс легким и быстрым. Внедрение современных решений позволяет предоставить прямой доступ к широкому ассортименту спортивных мероприятий с вашего мобильного. Скачать Olimp bet и благодаря последним обновлениям, вы насладитесь упрощенным управлением аккаунтом, понятным дизайном для легкости использования и повышенной производительностью приложения. Присоединяйтесь к сообществу поклонников БК Олимп, наслаждаясь возможностью делать ставки в любом месте и когда угодно. Установите актуальную версию приложения уже сейчас и выходите на новый уровень в мире ставок!
amitriptyline dosage for sleep
В ассортименте нашего интернет-магазина сантехники представлена только оригинальная продукция таких известных брендов как Джилекс, PRO AQUA, Valfex, LD, СТМ и многих других
does celebrex make you tired
is baclofen a narcotic or opiate
assumenda rem consequatur rerum. nisi alias id quasi libero. nihil cupiditate autem qui voluptates neque veniam consequatur. qui dolorem fuga possimus sint quia sit non sapiente molestiae aperiam qui aut. consectetur repellat perferendis officiis sit id dignissimos accusamus placeat et.
is augmentin good for uti
Ищете где купить копию Аирподс ПРО в Москве? Лучшие беспроводные наушники в Москве и области. Реплика оригинальных AirPods с активным шумоподавлением со скидкой. Надежные гарнитуры по низким ценам. Быстро доставим по России.
Ищете где купить реплику Airpods PRO в Москве? Качественные беспроводные наушники в Москве и РФ. Реплика оригинальных AirPods с активным шумоподавлением всего за 2490 рублей. Самые надежные гаджеты по низким ценам. Доставим по России.
В поисках где реплика Airpods PRO? Наилучшие беспроводные наушники в Москве и области. Реплика оригинальных AirPods с активным шумоподавлением по скидке. Самые качественные гаджеты по низким ценам. Быстрая доставка по России.
Ищете где копия Airpods PRO? Лучшие беспроводные наушники в Москве и РФ. Реплика оригинальных AirPods с шумоподавлением по скидке. Самые качественные гаджеты по приемлимым ценам. Доставка по России.
Вечно виснет и не грузится этот обзорник зевс техническое отставание.
Какой-то мутный обзорник зевс сплошь нелегальные казиношки продвигают.
Похоже админы явно за деньги впихивают левые обзоры от зевса.
Хорош уже рекламить casinozeus.by там такой высер рекомендуют крышу рвет просто.
Искали где реплика Airpods PRO? Наилучшие беспроводные наушники в Москве и области. Реплика оригинальных AirPods с шумоподавлением по скидке. Проверенные гарнитуры по доступным ценам. Быстро доставим по России.
Искали где купить копию Airpods PRO в Москве? Качественные беспроводные наушники в Москве. Реплика оригинальных AirPods с шумоподавлением всего за 2490 рублей. Самые качественные гаджеты по доступным ценам. Быстрая доставка по России.
Ищете где купить реплику Аирподс ПРО? Лучшие беспроводные наушники в Москве. Копия оригинальных AirPods с активным шумоподавлением всего за 2490 рублей. Только качественные гарнитуры по приемлимым ценам. Доставим по России.
В поисках где https://mdou41orel.ru/? Наилучшие беспроводные наушники в Москве. Реплика оригинальных AirPods с шумоподавлением всего за 2490 рублей. Самые качественные гаджеты по доступным ценам. Доставим по России.
Искали где реплика наушников Airpods PRO? Наилучшие беспроводные наушники в Москве. Реплика оригинальных AirPods с активным шумоподавлением по скидке. Надежные гаджеты по приемлимым ценам. Доставка по России.
В поисках где купить реплику Airpods PRO в Москве? Топовые беспроводные наушники в Москве. Копия оригинальных AirPods с активным шумоподавлением по скидке. Только проверенные гаджеты по низким ценам. Доставка по России.
Ищете где купить копию Airpods PRO в Москве? Лучшие беспроводные наушники в Москве. Реплика оригинальных AirPods с активным шумоподавлением по скидке. Надежные гаджеты по низким ценам. Доставка по России.
В поисках где копия Airpods PRO? Топовые беспроводные наушники в Москве и РФ. Реплика оригинальных AirPods с активным шумоподавлением по цене 2490 рублей. Только качественные гарнитуры по низким ценам. Доставка по России.
can i drink on bupropion
Одни проблемы. Приложение бк леон вылетает и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Приложение бк леон вылетает и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Программа бк леон не устанавливается и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. БК леон не работает и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Леон не работает приложение и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Программа бк леон не устанавливается и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Программа бк леон не устанавливается и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Приложение бк леон вылетает и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
В поисках где купить копию Airpods PRO? Качественные беспроводные наушники в Москве и области. Реплика оригинальных AirPods с активным шумоподавлением всего за 2490 рублей. Надежные гарнитуры по низким ценам. Быстрая доставка по России.
В поисках где купить реплику Airpods PRO? Лучшие беспроводные наушники в Москве. Копия оригинальных AirPods с активным шумоподавлением всего за 2490 рублей. Самые качественные гаджеты по приемлимым ценам. Быстро доставим по России.
В поисках где купить копию Airpods PRO в Москве? Наилучшие беспроводные наушники в Москве и РФ. Реплика оригинальных AirPods с шумоподавлением всего за 2490 рублей. Самые качественные гаджеты по доступным ценам. Доставка по России.
Искали где купить лучшую реплику Airpods PRO? Топовые беспроводные наушники в Москве. Реплика оригинальных AirPods с шумоподавлением со скидкой. Только качественные гарнитуры по доступным ценам. Быстро доставим по России.
Ищете где реплика наушников Airpods PRO? Лучшие беспроводные наушники в Москве и области. Копия оригинальных AirPods с шумоподавлением всего за 2490 рублей. Самые надежные гаджеты по низким ценам. Быстро доставим по России.
Искали где реплика наушников Airpods PRO? Наилучшие беспроводные наушники в Москве и РФ. Копия оригинальных AirPods с шумоподавлением по скидке. Самые качественные гаджеты по приемлимым ценам. Доставим по России.
В поисках где https://mdou41orel.ru/? Качественные беспроводные наушники в Москве и РФ. Копия оригинальных AirPods с шумоподавлением по скидке. Самые надежные гаджеты по низким ценам. Доставим по России.
Искали где копия наушников Airpods PRO? Качественные беспроводные наушники в Москве и области. Копия оригинальных AirPods с шумоподавлением по скидке. Проверенные гарнитуры по приемлимым ценам. Доставка по России.
Ищете где купить реплику наушников Airpods PRO в Москве? Наилучшие беспроводные наушники в Москве и области. Реплика оригинальных AirPods с шумоподавлением по скидке. Надежные гарнитуры по низким ценам. Доставка по России.
Ищете где купить реплику Аирподс ПРО в Москве? Качественные беспроводные наушники в Москве и РФ. Реплика оригинальных AirPods с активным шумоподавлением по цене 2490 рублей. Только проверенные гаджеты по приемлимым ценам. Быстрая доставка по России.
В поисках где el-gusto.ru? Топовые беспроводные наушники в Москве и области. Реплика оригинальных AirPods с шумоподавлением по цене 2490 рублей. Только качественные гарнитуры по приемлимым ценам. Доставим по России.
Искали где купить реплику наушников Airpods PRO в Москве? Качественные беспроводные наушники в Москве и области. Реплика оригинальных AirPods с активным шумоподавлением по цене 2490 рублей. Только качественные гаджеты по низким ценам. Быстро доставим по России.
Электронная регистрация в Росреестре – Сделки онлайн – Центр “Недвижимость и право”
Электронная регистрация в Росреестре сделок с недвижимостью. Ускоренные сроки – 3-7 дней. Выписки из ЕГРН.
Искали где купить реплику Airpods PRO в Москве? Качественные беспроводные наушники в Москве. Реплика оригинальных AirPods с активным шумоподавлением по скидке. Самые надежные гаджеты по приемлимым ценам. Быстро доставим по России.
В поисках где купить копию Аирподс ПРО? Лучшие беспроводные наушники в Москве и РФ. Реплика оригинальных AirPods с шумоподавлением со скидкой. Только проверенные гарнитуры по приемлимым ценам. Быстро доставим по России.
Ищете где купить лучшую реплику Airpods PRO? Качественные беспроводные наушники в Москве. Реплика оригинальных AirPods с шумоподавлением по цене 2490 рублей. Проверенные гаджеты по низким ценам. Быстрая доставка по России.
Уютные Квартиры посуточно в Симферополе
В поисках где купить реплику Аирподс ПРО? Лучшие беспроводные наушники в Москве. Реплика оригинальных AirPods с шумоподавлением по скидке. Надежные гаджеты по доступным ценам. Быстрая доставка по России.
celexa mg
Одни проблемы. Приложение леон ошибка и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Почему не работает бк леон сегодня и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Почему не работает приложение леон и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Программа бк леон не устанавливается и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Леон букмекерская не работает и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Леон букмекерская не работает и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Почему не работает бк леон и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Леон букмекерская не работает и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
Одни проблемы. Леон не работает приложение и с чем связана данная проблема я не знаю. Но лучше поискать другой источник для скачивания данной программы. Тут тратить свое время не советую.
iste est et delectus incidunt officiis maxime quis labore officiis sit aliquid quia voluptatum. soluta qui eos corporis ipsum atque optio libero ea fuga eius perspiciatis sed dolorem.
smoking while taking buspirone
1. Вибір натяжних стель – як правильно обрати?
2. Топ-5 популярних кольорів натяжних стель
3. Як зберегти чистоту натяжних стель?
4. Відгуки про натяжні стелі: плюси та мінуси
5. Як підібрати дизайн натяжних стель до інтер’єру?
6. Інноваційні технології у виробництві натяжних стель
7. Натяжні стелі з фотопечаттю – оригінальне рішення для кухні
8. Секрети вдалого монтажу натяжних стель
9. Як зекономити на встановленні натяжних стель?
10. Лампи для натяжних стель: які вибрати?
11. Відтінки синього для натяжних стель – ексклюзивний вибір
12. Якість матеріалів для натяжних стель: що обирати?
13. Крок за кроком: як самостійно встановити натяжні стелі
14. Натяжні стелі в дитячу кімнату: безпека та креативність
15. Як підтримувати тепло у приміщенні за допомогою натяжних стель
16. Вибір натяжних стель у ванну кімнату: практичні поради
17. Натяжні стелі зі структурним покриттям – тренд сучасного дизайну
18. Індивідуальність у кожному домашньому інтер’єрі: натяжні стелі з друком
19. Як обрати освітлення для натяжних стель: поради фахівця
20. Можливості дизайну натяжних стель: від класики до мінімалізму
натяжні стелі вартість http://www.natjazhnistelitvhyn.kiev.ua/ .
Здравствуйте! Предлагаем быстрый займ на карту в любое время. Вы можете получить средства без избыточных вопросов и документов. Приятные условия кредитования и срочное получение рядом с вами. Наберите нам для получения подробной информации, либо оставляйте заявку на сайте.
Приветствую! Предлагаем взять деньги срочно на карту в любом городе. Вы можете получить средства без избыточных вопросов и документов. Привлекательные условия кредитования и срочное получение рядом с вами. Звоните для получения подробной информации, или оставляйте заявку на сайте.
Всем привет! Предлагаем взять деньги срочно в Минске в любое время. Вы можете получить займ без избыточных вопросов и документов. Приятные условия кредитования и срочное получение в любом городе. Звоните для получения подробной информации, либо оставляйте заявку на сайте.
Здравствуйте! Предлагаю где можно взять займ рядом с вами. Вы можете получить средства без избыточных вопросов и документов. Приятные условия займа и быстрое получение в любом городе. Набирайте нам для получения подробной информации, или оставляйте заявку на сайте.
Здравствуйте! Возник вопрос про взять деньги прямо сейчас? Предоставляем безопасный источник финансовой помощи. Вы можете получить финансирование в займ без избыточных вопросов и документов? Тогда обратитесь к нам! Мы предоставляем выгодные условия займа, быстрое решение и гарантию конфиденциальности. Не откладывайте свои планы и мечты, воспользуйтесь нашим предложением прямо сейчас!
Привет! Возник вопрос про деньги в долг? Предоставляем безопасный источник финансовой помощи. Вы можете получить деньги в займ без избыточных вопросов и документов? Тогда обратитесь к нам! Мы предлагаем выгодные условия займа, моментальное решение и обеспечение конфиденциальности. Не откладывайте свои планы и мечты, воспользуйтесь нашим предложением прямо сейчас!
Привет! Появился вопрос про занять деньги? Предлагаем надежный источник финансовой помощи. Вы можете получить деньги в займ без избыточных вопросов и документов? Тогда обратитесь к нам! Мы предлагаем привлекательные условия займа, быстрое решение и обеспечение конфиденциальности. Не откладывайте свои планы и мечты, воспользуйтесь доступным предложением прямо сейчас!
Привет! Появился вопрос про занять деньги? Предоставляем надежный источник финансовой помощи. Вы можете получить средства в займ без избыточных вопросов и документов? Тогда обратитесь к нам! Мы готовы предоставить высокоприбыльные условия кредитования, быстрое решение и гарантию конфиденциальности. Не откладывайте свои планы и мечты, воспользуйтесь предложенным предложением прямо сейчас!
Всем привет! Предлагаю заем средств в любом городе. Вы можете получить займ без избыточных вопросов и документов. Привлекательные условия займа и быстрое получение в вашем городе. Набирайте нам для получения подробной информации, или оставляйте заявку на сайте.
Приветствую! Предлагаю взять деньги срочно в Минске в любое время. Вы можете получить деньги без лишних вопросов и документов. Приятные условия заема и срочное получение в вашем городе. Наберите нам для получения подробной информации, либо оставляйте заявку на сайте.
Всем привет! Предлагаю займы на карту в Минске круглосуточно. Вы можете получить средства без избыточных вопросов и документов. Достойные условия заема и срочное получение в вашем городе. Набирайте нам для уточнения подробной информации, или оставляйте заявку на сайте.
Здравствуйте! Предлагаю деньги в долг не банк в любом городе. Вы можете получить заем без излишних вопросов и документов. Приятные условия займа и срочное получение в любом городе. Наберите нам для уточнения подробной информации, или оставляйте заявку на сайте.
Здравствуйте! Возник вопрос про получить деньги в долг в городе? Предлагаем стабильный источник финансовой помощи. Вы можете получить финансирование в долг без избыточных вопросов и документов? Тогда обратитесь к нам! Мы готовы предоставить высокоприбыльные условия кредитования, оперативное решение и гарантию конфиденциальности. Не откладывайте свои планы и мечты, воспользуйтесь предложенным предложением прямо сейчас!
Всем привет! Возник вопрос про деньги в долг сегодня срочно? Предлагаем безопасный источник финансовой помощи. Вы можете получить финансирование в долг без избыточных вопросов и документов? Тогда обратитесь к нам! Мы готовы предоставить привлекательные условия займа, моментальное решение и гарантию конфиденциальности. Не откладывайте свои планы и мечты, воспользуйтесь предложенным предложением прямо сейчас!
Здравствуйте! Возник вопрос про где можно взять займ? Предлагаем стабильный источник финансовой помощи. Вы можете получить деньги в долг без излишних вопросов и документов? Тогда обратитесь к нам! Мы готовы предоставить высокоприбыльные условия займа, оперативное решение и обеспечение конфиденциальности. Не откладывайте свои планы и мечты, воспользуйтесь предложенным предложением прямо сейчас!
воєнторг
10. Распродажа военного снаряжения
армійський військторг воєнторг .
1. Почему берцы – это обязательный элемент стиля?
2. Как выбрать идеальные берцы для осеннего гардероба?
3. Тренды сезона: кожаные берцы или замшевые?
4. 5 способов носить берцы с платьем
5. Какие берцы выбрать для повседневного образа?
6. Берцы на платформе: комфорт и стиль в одном
7. Какие берцы будут актуальны в этом году?
8. Маст-хэв сезона: военные берцы в стиле милитари
9. 10 вариантов сочетания берцов с джинсами
10. Зимние берцы: как выбрать модель для холодного сезона
11. Элегантные берцы на каблуке: идеальный вариант для офиса
12. Секреты ухода за берцами: как сохранить первоначальный вид?
13. С какой юбкой носить берцы: советы от стилистов
14. Как подобрать берцы под фасон брюк?
15. Берцы на шнуровке: стильный акцент в образе
16. Берцы-челси: универсальная модель для любого стиля
17. С чем носить берцы на плоской подошве?
18. Берцы с ремешками: акцент на деталях
19. Как выбрать берцы для прогулок по городу?
20. Топ-5 брендов берцев: качество и стиль в одном
берці купити купити тактичні берці .
indikasi acarbose
semaglutide 0.75 mg
latuda vs abilify
great article
Официальные дилеры и сервисные центры
bmw x5 2023 bmw i 7 .
remeron 15 mg side effects
is robaxin 500 mg a narcotic
купить плинтус алюминиевый плинтус цена .
1. Как выбрать идеальный гипсокартон для ремонта
стяжка пола строительные материалы в москве .
repaglinide transdermal patch
прогулочные коляски москва для детей коляски .
Поради стоматолога
6. Як вибрати найкращий зубний пасти зі змістом фтору
послуги стоматології послуги стоматології .
1. 10 лучших идей для дизайна интерьера
2. Топ-20 трендов в дизайне на 2021 год
3. Как выбрать идеальный цветовой акцент в дизайне
4. Дизайн-проект
5. Дизайн нового поколения
6. Шаг за шагом: создание уютного дизайна спальни
7. Дизайнерские решения для увеличения пространства в маленькой квартире
8. Природный дизайн
9. Баланс цветов и форм: основы хорошего дизайна
10. Дизайн-студия: секреты успешного бизнеса в сфере дизайна
11. Интересные факты о развитии дизайна в XXI веке
12. Уникальные идеи для дизайна кухни: создайте пространство своей мечты
13. Тенденции в сфере дизайна мебели: вдохновляющие идеи
14. Мастер-класс по созданию стильного дизайна гостиной
15. Минимализм
16. Дизайн сада
17. Декорирование дома с использованием текстиля: советы и идеи
18. Принципы цветового баланса в дизайне: как создать гармоничное пространство
19. Топ-10 книг по дизайну интерьера, которые стоит прочитать
20. Дизайн комнаты для подростка: креативные идеи для стильного интерьера
студия дизайна и интерьера студия дизайна и интерьера .
купить сплит систему в москве https://split-sistema-kupit.ru/ .
В настоящее время наши дни могут содержать неожиданные расходы и экономические трудности, и в такие моменты каждый ищет надежную поддержку. На сайте brokers-group.ru вам помогут без лишних сложностей. В своей роли представителя я стремлюсь поделиться этими сведениями, чтобы помочь тем, кто столкнулся с временными трудностями. Наша платформа обеспечивает прозрачные условия и эффективное рассмотрение запросов, чтобы каждый мог решить свои денежные проблемы быстро и без лишних хлопот.
В настоящее время наши дни могут содержать внезапные издержки и экономические трудности, и в такие моменты каждый ищет надежную поддержку. На сайте деньги в долг в Минске вам помогут без избыточной бюрократии. В своей роли агента я стремлюсь распространить эту информацию, чтобы помочь тем, кто столкнулся с временными трудностями. Наша система обеспечивает честные условия и быструю обработку заявок, чтобы каждый мог разрешить свои финансовые вопросы оперативно и без лишних затрат времени.
В настоящее время наши дни могут содержать внезапные издержки и экономические трудности, и в такие моменты каждый ищет надежную поддержку. На сайте деньги в долг вам помогут без избыточной бюрократии. В своей роли агента я стремлюсь поделиться этими сведениями, чтобы помочь людям в сложной ситуации. Наша платформа обеспечивает честные условия и эффективное рассмотрение запросов, чтобы каждый мог разрешить свои финансовые вопросы оперативно и без лишних затрат времени.
В настоящее время наши дни могут содержать внезапные издержки и финансовые вызовы, и в такие моменты каждый ищет надежную поддержку. На сайте деньги в долг вам помогут без лишних сложностей. В своей роли агента я стремлюсь поделиться этими сведениями, чтобы помочь тем, кто столкнулся с временными трудностями. Наша система обеспечивает честные условия и быструю обработку заявок, чтобы каждый мог разрешить свои финансовые вопросы оперативно и без лишних затрат времени.
В наше время многие из нас сталкиваются с внезапными затратами и денежными трудностями, и в такие моменты важно иметь доступ к дополнительным средствам. На сайте деньги в кредит вам помогут с минимальными усилиями. В качестве официального представителя Брокерс Групп, я рад делиться этой информацией, чтобы помочь каждому, кто столкнулся с финансовыми трудностями. Наша платформа гарантирует прозрачные условия и оперативное рассмотрение запросов, чтобы каждый мог решить свои финансовые вопросы с минимальными временными затратами.
В наше время многие из нас сталкиваются с внезапными затратами и денежными трудностями, и в такие моменты важно иметь возможность взять кредит. На сайте займ денег вам помогут с минимальными усилиями. В качестве официального представителя Брокерс Групп, я рад делиться этой информацией, чтобы помочь каждому, кто нуждается в финансовой поддержке. Наша платформа гарантирует честные условия и быструю обработку заявок, чтобы каждый мог решить свои финансовые вопросы с минимальными временными затратами.
В наше время многие из нас сталкиваются с непредвиденными расходами и денежными трудностями, и в такие моменты важно иметь возможность взять кредит. На сайте займ на карту без отказа вам помогут с минимальными усилиями. В качестве официального представителя Брокерс Групп, я с удовольствием делиться этой информацией, чтобы помочь людям, кто столкнулся с финансовыми трудностями. Наша платформа гарантирует честные условия и быструю обработку заявок, чтобы каждый мог разрешить свои денежные проблемы с минимальными временными затратами.
В наше время многие из нас сталкиваются с непредвиденными расходами и денежными трудностями, и в такие моменты важно иметь доступ к дополнительным средствам. На сайте взять деньги в долг вам помогут быстро и удобно. В качестве официального представителя Брокерс Групп, я с удовольствием делиться этой информацией, чтобы помочь людям, кто нуждается в финансовой поддержке. Наша платформа гарантирует честные условия и быструю обработку заявок, чтобы каждый мог разрешить свои денежные проблемы с минимальными временными затратами.
В настоящей эпохе финансовые трудности не редкость, и каждый из нас может оказаться в ситуации, когда необходима дополнительная финансовая поддержка. На сайте займ в беларуси помогут преодолеть эти трудности, предоставляя простой и лёгкий метод займа. Мы осознаём, что время играет ключевую роль, поэтому мы обрабатываем заявки оперативно и эффективно. В роли представителя Манибел, мы нацелены на то, чтобы помочь каждому клиенту преодолеть свои денежные трудности, предоставив прозрачные и выгодные условия кредитования. Доверьтесь нам, и мы решим ваши финансовые проблемы.
В настоящей эпохе финансовые сложности не редкость, и каждый человек может оказаться в ситуации, когда необходима дополнительная финансовая поддержка. На сайте займы онлайн помогут решить эти проблемы, предоставляя простой и лёгкий метод займа. Мы осознаём, что времени на решение проблемы не хватает, поэтому мы обрабатываем заявки оперативно и эффективно. В качестве представителя Манибел, мы нацелены на то, чтобы помочь каждому клиенту преодолеть свои денежные трудности, предложив ясные и выгодные условия займа. Доверьтесь нашей компании, и мы решим ваши финансовые проблемы.
В настоящей эпохе финансовые сложности встречаются часто, и каждый из нас может оказаться в ситуации, когда необходима дополнительная финансовая поддержка. На сайте деньги в долг помогут преодолеть эти трудности, предоставляя простой и удобный способ получения кредита. Мы понимаем, что время играет ключевую роль, поэтому мы обрабатываем заявки оперативно и эффективно. В качестве представителя Манибел, мы нацелены на то, чтобы помочь каждому клиенту преодолеть свои денежные трудности, предоставив прозрачные и выгодные условия кредитования. Доверьтесь нашей компании, и мы решим ваши финансовые проблемы.
В настоящей эпохе финансовые трудности встречаются часто, и каждый человек может оказаться в ситуации, когда необходима дополнительная финансовая поддержка. На сайте получить деньги в долг в Минске помогут преодолеть эти трудности, предоставляя простой и удобный способ получения кредита. Мы осознаём, что времени на решение проблемы не хватает, поэтому наш процесс обработки заявок максимально быстр и эффективен. В роли представителя Манибел, наша цель – помочь каждому клиенту преодолеть финансовые затруднения, предоставив прозрачные и выгодные условия кредитования. Доверьтесь нам, и мы поможем вам в решении ваших финансовых проблем.
canadian pharmacy cialis
В настоящей экономической обстановке, где неожиданные финансовые обязательства могут возникнуть в любое время, поиск надежного и удобного источника финансовой помощи становится все более критическим. Предложение займы онлайн на карту предлагает возможность рассчитывать на быстрое и беззаботное получение необходимых средств без лишних трудностей. Мы ценим ваше время и обеспечиваем оперативную обработку всех запросов. В качестве вашего финансового партнера, наша главная задача состоит в том, чтобы помочь вам преодолеть текущие финансовые препятствия, предоставляя ясные и выгодные условия кредитования. Доверьтесь нам в вашем финансовом путешествии, и мы обеспечим вас надежной поддержкой на каждом этапе.
В настоящей экономической обстановке, где неожиданные финансовые обязательства могут возникнуть в любое время, поиск надежного и удобного источника финансовой помощи становится все более критическим. Предложение деньги в долг в Минске срочно предлагает возможность рассчитывать на быстрое и беззаботное получение необходимых средств без лишних трудностей. Мы ценим ваше время и обеспечиваем оперативную обработку всех запросов. В качестве вашего финансового партнера, наша главная задача состоит в том, чтобы помочь вам преодолеть текущие финансовые препятствия, предоставляя ясные и выгодные условия кредитования. Доверьтесь нам в вашем финансовом путешествии, и мы обеспечим вас надежной поддержкой на каждом этапе.
В настоящей экономической обстановке, где неожиданные финансовые обязательства могут возникнуть в любое время, поиск надежного и удобного источника финансовой помощи становится все более критическим. Предложение быстрый займ предлагает возможность рассчитывать на быстрое и беззаботное получение необходимых средств без лишних трудностей. Мы ценим ваше время и обеспечиваем оперативную обработку всех запросов. В качестве вашего финансового партнера, наша главная задача состоит в том, чтобы помочь вам преодолеть текущие финансовые препятствия, предоставляя ясные и выгодные условия кредитования. Доверьтесь нам в вашем финансовом путешествии, и мы обеспечим вас надежной поддержкой на каждом этапе.
В настоящей экономической обстановке, где неожиданные финансовые обязательства могут возникнуть в любое время, поиск надежного и удобного источника финансовой помощи становится все более критическим. Предложение деньги в долг предлагает возможность рассчитывать на быстрое и беззаботное получение необходимых средств без лишних трудностей. Мы ценим ваше время и обеспечиваем оперативную обработку всех запросов. В качестве вашего финансового партнера, наша главная задача состоит в том, чтобы помочь вам преодолеть текущие финансовые препятствия, предоставляя ясные и выгодные условия кредитования. Доверьтесь нам в вашем финансовом путешествии, и мы обеспечим вас надежной поддержкой на каждом этапе.
Шаг за шагом: установка кондиционера своими руками
инверторный кондиционер https://ustanovka-kondicionera-cena.ru/ .
1. Как установить кондиционер в доме
обслуживание кондиционеров и вентиляции https://prodazha-kondcionerov.ru/ .
В настоящее время наши дни могут содержать неожиданные расходы и экономические трудности, и в такие моменты каждый ищет надежную поддержку. На сайте займ онлайн вам помогут без избыточной бюрократии. В своей роли агента я стремлюсь поделиться этими сведениями, чтобы помочь тем, кто столкнулся с временными трудностями. Наша система обеспечивает честные условия и эффективное рассмотрение запросов, чтобы каждый мог решить свои денежные проблемы быстро и без лишних хлопот.
В настоящее время наши дни могут содержать внезапные издержки и финансовые вызовы, и в такие моменты каждый ищет надежную поддержку. На сайте взять деньги в кредит вам помогут без избыточной бюрократии. В своей роли представителя я стремлюсь распространить эту информацию, чтобы помочь тем, кто столкнулся с временными трудностями. Наша система обеспечивает прозрачные условия и эффективное рассмотрение запросов, чтобы каждый мог решить свои денежные проблемы быстро и без лишних хлопот.
В настоящее время наши дни могут содержать внезапные издержки и экономические трудности, и в такие моменты каждый ищет помощь. На сайте brokers-group.ru вам помогут без лишних сложностей. В своей роли агента я стремлюсь распространить эту информацию, чтобы помочь людям в сложной ситуации. Наша платформа обеспечивает прозрачные условия и быструю обработку заявок, чтобы каждый мог решить свои денежные проблемы быстро и без лишних хлопот.
В настоящее время наши дни могут содержать неожиданные расходы и финансовые вызовы, и в такие моменты каждый ищет помощь. На сайте получить деньги вам помогут без избыточной бюрократии. В своей роли представителя я стремлюсь распространить эту информацию, чтобы помочь людям в сложной ситуации. Наша платформа обеспечивает честные условия и эффективное рассмотрение запросов, чтобы каждый мог решить свои денежные проблемы оперативно и без лишних затрат времени.
remeron sleeping pill
В наше время многие из нас сталкиваются с непредвиденными расходами и экономическими вызовами, и в такие моменты важно иметь доступ к дополнительным средствам. На сайте деньги в долг на карту вам помогут быстро и удобно. В качестве представителя Брокерс Групп, я с удовольствием делиться этой информацией, чтобы помочь каждому, кто столкнулся с финансовыми трудностями. Наша система гарантирует прозрачные условия и оперативное рассмотрение запросов, чтобы каждый мог разрешить свои денежные проблемы с минимальными временными затратами.
В наше время многие из нас сталкиваются с непредвиденными расходами и экономическими вызовами, и в такие моменты важно иметь доступ к дополнительным средствам. На сайте ДеньгиЗаймы вам помогут быстро и удобно. В качестве официального представителя Брокерс Групп, я с удовольствием делиться этой информацией, чтобы помочь каждому, кто нуждается в финансовой поддержке. Наша система гарантирует прозрачные условия и оперативное рассмотрение запросов, чтобы каждый мог разрешить свои денежные проблемы быстро и эффективно.
В наше время многие из нас сталкиваются с непредвиденными расходами и денежными трудностями, и в такие моменты важно иметь доступ к дополнительным средствам. На сайте получить займ в Минске вам помогут с минимальными усилиями. В качестве официального представителя Брокерс Групп, я рад делиться этой важной информацией, чтобы помочь людям, кто нуждается в финансовой поддержке. Наша система гарантирует прозрачные условия и оперативное рассмотрение запросов, чтобы каждый мог решить свои финансовые вопросы с минимальными временными затратами.
В наше время многие из нас сталкиваются с непредвиденными расходами и денежными трудностями, и в такие моменты важно иметь доступ к дополнительным средствам. На сайте займы онлайн на карту вам помогут быстро и удобно. В качестве представителя Брокерс Групп, я с удовольствием делиться этой важной информацией, чтобы помочь людям, кто нуждается в финансовой поддержке. Наша платформа гарантирует честные условия и быструю обработку заявок, чтобы каждый мог разрешить свои денежные проблемы с минимальными временными затратами.
В настоящей эпохе финансовые сложности встречаются часто, и каждый из нас может оказаться в ситуации, когда потребуется дополнительная финансовая помощь. На сайте [url=https://moneybel.ru/]деньги в кредит[/url] помогут преодолеть эти трудности, принося простой и лёгкий метод займа. Мы осознаём, что времени на решение проблемы не хватает, поэтому наш процесс обработки заявок максимально быстр и эффективен. В качестве представителя Манибел, наша цель – помочь каждому клиенту преодолеть финансовые затруднения, предложив ясные и выгодные условия займа. Доверьтесь нам, и мы решим ваши финансовые проблемы.
В сегодняшнем обществе финансовые сложности не редкость, и каждый человек может оказаться в ситуации, когда необходима дополнительная финансовая поддержка. На сайте получить деньги в долг в Минске помогут решить эти проблемы, предоставляя простой и удобный способ займа. Мы понимаем, что времени на решение проблемы не хватает, поэтому мы обрабатываем заявки оперативно и эффективно. В роли представителя Манибел, наша цель – помочь каждому клиенту преодолеть финансовые затруднения, предоставив прозрачные и выгодные условия кредитования. Доверьтесь нам, и мы решим ваши финансовые проблемы.
non-prescription synthroid
В настоящей эпохе финансовые трудности не редкость, и каждый человек может оказаться в ситуации, когда потребуется дополнительная финансовая помощь. На сайте получить займ в Минске помогут решить эти проблемы, принося простой и удобный способ получения кредита. Мы понимаем, что времени на решение проблемы не хватает, поэтому мы обрабатываем заявки оперативно и эффективно. В роли представителя Манибел, наша цель – помочь каждому клиенту преодолеть финансовые затруднения, предложив ясные и выгодные условия займа. Доверьтесь нашей компании, и мы решим ваши финансовые проблемы.
В настоящей эпохе финансовые трудности встречаются часто, и каждый человек может оказаться в ситуации, когда необходима дополнительная финансовая поддержка. На сайте займы онлайн на карту помогут преодолеть эти трудности, предоставляя простой и удобный способ займа. Мы понимаем, что время играет ключевую роль, поэтому наш процесс обработки заявок максимально быстр и эффективен. В качестве представителя Манибел, мы нацелены на то, чтобы помочь каждому клиенту преодолеть свои денежные трудности, предоставив прозрачные и выгодные условия кредитования. Доверьтесь нашей компании, и мы поможем вам в решении ваших финансовых проблем.
В настоящей экономической обстановке, где неожиданные финансовые обязательства могут возникнуть в любое время, поиск надежного и удобного источника финансовой помощи становится все более критическим. Предложение займ денег предлагает возможность рассчитывать на быстрое и беззаботное получение необходимых средств без лишних трудностей. Мы ценим ваше время и обеспечиваем оперативную обработку всех запросов. В качестве вашего финансового партнера, наша главная задача состоит в том, чтобы помочь вам преодолеть текущие финансовые препятствия, предоставляя ясные и выгодные условия кредитования. Доверьтесь нам в вашем финансовом путешествии, и мы обеспечим вас надежной поддержкой на каждом этапе.
В настоящей экономической обстановке, где неожиданные финансовые обязательства могут возникнуть в любое время, поиск надежного и удобного источника финансовой помощи становится все более критическим. Предложение займы онлайн предлагает возможность рассчитывать на быстрое и беззаботное получение необходимых средств без лишних трудностей. Мы ценим ваше время и обеспечиваем оперативную обработку всех запросов. В качестве вашего финансового партнера, наша главная задача состоит в том, чтобы помочь вам преодолеть текущие финансовые препятствия, предоставляя ясные и выгодные условия кредитования. Доверьтесь нам в вашем финансовом путешествии, и мы обеспечим вас надежной поддержкой на каждом этапе.
В настоящей экономической обстановке, где неожиданные финансовые обязательства могут возникнуть в любое время, поиск надежного и удобного источника финансовой помощи становится все более критическим. Предложение быстрый займ предлагает возможность рассчитывать на быстрое и беззаботное получение необходимых средств без лишних трудностей. Мы ценим ваше время и обеспечиваем оперативную обработку всех запросов. В качестве вашего финансового партнера, наша главная задача состоит в том, чтобы помочь вам преодолеть текущие финансовые препятствия, предоставляя ясные и выгодные условия кредитования. Доверьтесь нам в вашем финансовом путешествии, и мы обеспечим вас надежной поддержкой на каждом этапе.
В настоящей экономической обстановке, где неожиданные финансовые обязательства могут возникнуть в любое время, поиск надежного и удобного источника финансовой помощи становится все более критическим. Предложение взять деньги в долг предлагает возможность рассчитывать на быстрое и беззаботное получение необходимых средств без лишних трудностей. Мы ценим ваше время и обеспечиваем оперативную обработку всех запросов. В качестве вашего финансового партнера, наша главная задача состоит в том, чтобы помочь вам преодолеть текущие финансовые препятствия, предоставляя ясные и выгодные условия кредитования. Доверьтесь нам в вашем финансовом путешествии, и мы обеспечим вас надежной поддержкой на каждом этапе.
Внимание, любители ставок! БК Олимп представляет с гордостью последнюю версию своего приложения для Android, которое обещает перевернуть ваш мир ставок на радость. Мы полностью пересмотрели приложение, чтобы гарантировать лучший опыт от ставок на спорт. Букмекерская контора Олимп на андроид и откройте доступ к широкому спектру спортивных событий, который стал удобнее благодаря новому дизайну и оптимизированной производительности данных. Присоединяйтесь к сообществу БК Олимп и пользуйтесь возможностью делать ставки где угодно, будь то дома или в путешествии. Получите новую версию приложения без задержек и откройте для себя мир ставок с БК Олимп, где победы становятся реальностью!
Внимание, любители ставок! БК Олимп представляет с гордостью новейшую версию своего приложения для Android, которое обещает изменить ваш мир ставок на радость. Мы полностью пересмотрели приложение, чтобы предоставить вам несравненный опыт от ставок на спорт. Olimp bet на андроид и откройте доступ к широкому спектру спортивных событий, который стал проще благодаря улучшенному интерфейсу и оптимизированной производительности данных. Подключайтесь к нам и пользуйтесь возможностью делать ставки где угодно, будь то на диване или в отпуске. Загрузите новую версию приложения прямо сейчас и погрузитесь в мир ставок с БК Олимп, где выигрыши становятся реальностью!
Внимание, любители ставок! БК Олимп представляет с гордостью последнюю версию своего приложения для Android, которое обещает перевернуть ваш мир ставок к лучшему. Мы полностью пересмотрели приложение, чтобы предоставить вам лучший опыт от ставок на спорт. Олимп на андроид и откройте доступ к широкому спектру спортивных событий, который стал проще благодаря новому дизайну и ускоренной обработке данных. Присоединяйтесь к сообществу БК Олимп и наслаждайтесь возможностью делать ставки где угодно, будь то на диване или в отпуске. Получите новую версию приложения прямо сейчас и откройте для себя мир ставок с БК Олимп, где победы становятся реальностью!
кондиционер инвертор кондиционер инвертор .
Внимание, любители ставок! БК Олимп представляет с гордостью последнюю версию своего приложения для Android, которое обещает изменить ваш мир ставок к лучшему. Мы полностью пересмотрели приложение, чтобы гарантировать лучший опыт от ставок на спорт. Olimp bet приложение и откройте доступ к широкому спектру спортивных событий, который стал удобнее благодаря улучшенному интерфейсу и ускоренной обработке данных. Подключайтесь к нам и наслаждайтесь возможностью делать ставки где угодно, будь то на диване или в отпуске. Получите новую версию приложения прямо сейчас и погрузитесь в мир ставок с БК Олимп, где победы становятся реальностью!
Вот оно, свежее веяние от БК Олимп для всех поклонников ставок с Android устройствами! Изменив наше приложение, мы стремимся предоставить вам непревзойденный опыт, делая ставки не только простыми, но и захватывающими. Скачать БК Олимп для андроид доступно для игроков! С улучшенным интерфейсом и быстрой обработкой данных, доступ к большому разнообразию событий стал легким делом. Ощутите радость от улучшенного управления счетом и простоты использования, которые делают каждую ставку особым событием. Забудьте о пропущенных возможностях – скачайте последнее обновление сейчас же и присоединитесь к довольных пользователей, празднующих каждой ставке с БК Олимп, где каждый шанс на победу ценится.
Вот оно, свежее веяние от БК Олимп для всех поклонников ставок с Android устройствами! Изменив наше приложение, мы стремимся предоставить вам уникальный опыт, делая ставки не только удобными, но и захватывающими. Букмекерская контора Олимп для андроид доступно для игроков! С новым дизайном и быстрой обработкой данных, доступ к большому разнообразию событий стал проще простого. Испытайте радость от улучшенного управления счетом и интуитивной навигации, которые делают каждую ставку волнующим моментом. Не упустите возможностях – установите последнее обновление сейчас же и вступите в ряды довольных пользователей, празднующих каждой ставке с БК Олимп, где каждый шанс на победу ценится.
Вот оно, свежее веяние от БК Олимп для всех поклонников ставок с Android устройствами! Изменив наше приложение, мы стремимся предоставить вам уникальный опыт, делая ставки не только простыми, но и захватывающими. Скачать Olimp возможно сегодня! С улучшенным интерфейсом и быстрой обработкой данных, доступ к огромному спектру событий стал легким делом. Испытайте радость от улучшенного управления счетом и интуитивной навигации, которые делают каждую ставку волнующим моментом. Не упустите возможностях – скачайте последнее обновление немедленно и присоединитесь к довольных пользователей, радующихся каждой ставке с БК Олимп, где каждый шанс на победу ценится.
Вот оно, свежее веяние от БК Олимп для всех поклонников ставок с Android устройствами! Преобразив наше приложение, мы целимся предоставить вам непревзойденный опыт, делая ставки не только удобными, но и захватывающими. Скачать приложение БК Олимп доступно для игроков! С улучшенным интерфейсом и быстрой обработкой данных, доступ к огромному спектру событий стал легким делом. Испытайте радость от оптимизированной работы с аккаунтом и простоты использования, которые делают каждую ставку особым событием. Забудьте о пропущенных возможностях – установите последнее обновление немедленно и вступите в ряды довольных пользователей, празднующих каждой ставке с БК Олимп, где каждый шанс на победу высоко оценивается.
Не пропустите новинку от БК Олимп для Android! Скачать Olimp возможно сегодня. Мы пересмотрели наше приложение, чтобы ваш опыт ставок стал ещё лучше. С переработанным дизайном и повышенной скоростью, вы получите доступ к широкому ассортименту спортивных событий без усилий. Наслаждайтесь простотой управления аккаунтом и интуитивной навигацией, делая каждую ставку особым моментом. Загрузите это обновление сегодня и начните побеждать с БК Олимп, где каждая ставка приносит удовольствие!
Не пропустите обновление от БК Олимп для Android! Скачать Olimp bet на андроид возможно сегодня. Мы пересмотрели наше приложение, чтобы ваш опыт ставок стал ещё удобнее. С новым интерфейсом и ускоренной обработкой данных, вы получите доступ к широкому ассортименту спортивных событий без усилий. Наслаждайтесь простотой управления аккаунтом и лёгкостью использования, делая каждую ставку значимым событием. Загрузите это обновление сегодня и стартуйте побеждать с БК Олимп, где каждая ставка приносит удовольствие!
Не пропустите обновление от БК Олимп для Android! Приложение Олимп бет на андроид доступно сейчас. Мы обновили наше приложение, чтобы ваш опыт ставок стал ещё лучше. С новым интерфейсом и ускоренной обработкой данных, вы получите доступ к широкому ассортименту спортивных событий без усилий. Оцените простотой управления аккаунтом и интуитивной навигацией, делая каждую ставку значимым событием. Загрузите это приложение прямо сейчас и начните выигрывать с БК Олимп, где каждая ставка приносит радость!
Не пропустите новинку от БК Олимп для Android! Скачать приложение Олимп на андроид доступно сейчас. Мы обновили наше приложение, чтобы ваш опыт ставок стал ещё лучше. С новым интерфейсом и повышенной скоростью, вы получите доступ к широкому ассортименту спортивных событий легко и просто. Наслаждайтесь удобством ведения счета и лёгкостью использования, делая каждую ставку значимым событием. Установите это обновление сегодня и начните выигрывать с БК Олимп, где каждая ставка приносит радость!
Запуск переделанной версии приложения БК Олимп для Android уже здесь! Переосмыслив функционал, мы сделали процесс ставок невероятно простым. БК Олимп на андроид доступно для ставочников. С обновленным дизайном и быстрой обработкой, доступ к всему спектру спортивных событий станет легкостью. Наслаждайтесь простотой управления счетом и легкой навигацией, превращая каждую ставку в важное событие. Не задерживайтесь, скачайте последнюю версию прямо сейчас и присоединяйтесь к победителям с БК Олимп, где ставки приносят удовольствие и победы!
Запуск обновленной версии приложения БК Олимп для Android уже здесь! Модернизировав функционал, мы сделали процесс ставок еще более увлекательным. Скачать БК Олимп на андроид доступно для ставочников. С обновленным дизайном и ускоренной загрузкой данных, доступ к всему спектру спортивных событий станет легкостью. Ощутите удобство управления счетом и легкой навигацией, превращая каждую ставку в особенный момент. Не теряйте времени, получите последнюю версию без отлагательств и присоединяйтесь к удовлетворенным пользователям с БК Олимп, где ставки приносят наслаждение и победы!
Запуск переделанной версии приложения БК Олимп для Android уже здесь! Переосмыслив функционал, мы сделали процесс ставок еще более увлекательным. Скачать Олимп бет на андроид доступно для ставочников. С передовым интерфейсом и быстрой обработкой, доступ к всему спектру спортивных событий станет игрой. Наслаждайтесь простотой управления счетом и легкой навигацией, превращая каждую ставку в особенный момент. Не теряйте времени, получите последнюю версию прямо сейчас и присоединяйтесь к удовлетворенным пользователям с БК Олимп, где ставки приносят удовольствие и победы!
Запуск обновленной версии приложения БК Олимп для Android уже здесь! Модернизировав функционал, мы сделали процесс ставок невероятно простым. Приложение Olimp bet доступное для игроков. С обновленным дизайном и ускоренной загрузкой данных, доступ к всему спектру спортивных событий станет игрой. Ощутите удобство управления счетом и легкой навигацией, превращая каждую ставку в особенный момент. Не задерживайтесь, скачайте последнюю версию без отлагательств и присоединяйтесь к удовлетворенным пользователям с БК Олимп, где ставки приносят наслаждение и победы!
Откройте для себя новейшие обновления в приложении БК Олимп для Android! Скачать БК Олимп на андроид доступно сегодня. Мы совершенствовали наше приложение, чтобы сделать ваше взаимодействие с ставками удобным. С новым дизайном и ускоренной обработке данных, вы теперь имеете легкий доступ к широкому спектру спортивных событий. Оцените удобство использования своим аккаунтом и легкость управления, превращая каждую вашу ставку в значимое событие. Получите приложение прямо сегодня и начните зарабатывать на своих победах вместе с БК Олимп, где каждая ставка несет радость.
Откройте для себя последние новшества в приложении БК Олимп для Android! Olimp bet приложение доступно сейчас. Мы улучшили наше приложение, чтобы сделать ваше взаимодействие с ставками удобным. С новым дизайном и быстрой загрузке данных, вы теперь имеете прямой доступ к широкому спектру спортивных событий. Научитесь наслаждаться простоту управления своим аккаунтом и легкость управления, превращая каждую вашу ставку в уникальное приключение. Получите приложение сейчас и начните зарабатывать на своих победах вместе с БК Олимп, где каждая ставка принесет успех.
Откройте для себя последние новшества в приложении БК Олимп для Android! Скачать приложение Олимп бет доступно сегодня. Мы совершенствовали наше приложение, чтобы сделать ваше взаимодействие с ставками удобным. Благодаря усовершенствованному интерфейсу и ускоренной обработке данных, вы теперь имеете легкий доступ к широкому ассортименту спортивных событий. Научитесь наслаждаться простоту управления своим аккаунтом и легкость управления, превращая каждую вашу ставку в значимое событие. Получите приложение прямо сегодня и начните получать удовольствие от побед вместе с БК Олимп, где каждая ставка несет радость.
Откройте для себя новейшие обновления в приложении БК Олимп для Android! Приложение букмекерской конторы Олимп доступное для игроков. Мы совершенствовали наше приложение, чтобы сделать ваше взаимодействие с ставками более приятным. Благодаря усовершенствованному интерфейсу и ускоренной обработке данных, вы теперь имеете прямой доступ к широкому спектру спортивных событий. Оцените удобство использования своим аккаунтом и интуитивную навигацию, превращая каждую вашу ставку в уникальное приключение. Загрузите обновление прямо сегодня и начните зарабатывать на своих победах вместе с БК Олимп, где каждая ставка принесет успех.
Откройте для себя революцию в мире ставок с последним обновлением приложения БК Олимп для Android! Скачать приложение БК Олимп уже сейчас. Мы освежили приложение, обеспечивая беспрецедентный уровень удобства и быстроту загрузки. Теперь разнообразие спортивных событий находится у вас под рукой с улучшенным дизайном и легкой навигацией. Прочувствуйте на себе легкость управления счетом и сделайте каждую ставку значительным событием. Загрузите это приложение сегодня и поднимайте свой опыт ставок с БК Олимп, где каждый выбор может принести победу!
Откройте для себя новшество в мире ставок с новейшей версией приложения БК Олимп для Android! Скачать Олимп бет прямо сейчас. Мы полностью переработали приложение, обеспечивая неимоверную простоту использования и быстроту загрузки. Теперь выбор соревнований находится у вас под рукой с улучшенным дизайном и легкой навигацией. Испытайте на себе простоту ведения финансов и сделайте каждую ставку незабываемым моментом. Установите это приложение сегодня и поднимайте свой опыт ставок с БК Олимп, где каждый выбор может принести успех!
Откройте для себя революцию в мире ставок с последним обновлением приложения БК Олимп для Android! Скачать контору Олимп на андроид уже сейчас. Мы полностью переработали приложение, обеспечивая беспрецедентный уровень удобства и скорость доступа. Теперь выбор соревнований находится у вас под рукой с новым дизайном и интуитивной навигацией. Прочувствуйте на себе простоту ведения финансов и сделайте каждую ставку незабываемым моментом. Установите это приложение сегодня и поднимайте свой опыт ставок с БК Олимп, где каждый выбор может принести успех!
Інноваційні технології в тактичних кросівках
кросівки тактичні військові https://vijskovikrosivkifvgh.kiev.ua/ .
Откройте для себя новшество в мире ставок с последним обновлением приложения БК Олимп для Android! Olimp для андроид сегодня и сейчас. Мы освежили приложение, обеспечивая неимоверную простоту использования и скорость доступа. Теперь разнообразие спортивных событий находится у вас под рукой с улучшенным дизайном и интуитивной навигацией. Прочувствуйте на себе простоту ведения финансов и сделайте каждую ставку незабываемым моментом. Установите это приложение сегодня и выходите на новый уровень ставок с БК Олимп, где каждый выбор может принести победу!
Познакомьтесь с свежим обновлением приложения БК Олимп для Android, изменяющим ваш опыт в мире ставок! Приложение Olimp на андроид доступны сегодня для каждого. Передовой дизайн и быстрая загрузка данных обеспечивают легкий доступ к широкому ассортименту спортивных событий. Кастомизируйте свой аккаунт с уникальной простотой и навигацией, превращая каждую ставку в волнующее приключение. Загрузите сейчас и начните получать удовольствие от ставок на новом уровне с БК Олимп, где каждое событие – это шанс на выигрыш!
Познакомьтесь с свежим обновлением приложения БК Олимп для Android, изменяющим ваш опыт в мире ставок! Приложение букмекерской конторы Олимп доступны для всех ставочников. Инновационный дизайн и быстрая загрузка данных обеспечивают легкий доступ к множеству спортивных событий. Настройте свой аккаунт с непревзойденной легкостью и навигацией, превращая каждую ставку в волнующее приключение. Скачайте сейчас и начните получать удовольствие от ставок на новом уровне с БК Олимп, где каждое событие – это шанс на успех!
Познакомьтесь с свежим обновлением приложения БК Олимп для Android, изменяющим ваш опыт в мире ставок! Приложение Olimp доступны всем игрокам. Инновационный дизайн и быстрая загрузка данных обеспечивают легкий доступ к множеству спортивных событий. Настройте свой аккаунт с непревзойденной легкостью и навигацией, превращая каждую ставку в волнующее приключение. Скачайте сейчас и начните получать удовольствие от ставок на новом уровне с БК Олимп, где каждое событие – это шанс на выигрыш!
Познакомьтесь с новейшим обновлением приложения БК Олимп для Android, преобразующим ваш опыт в мире ставок! Скачать БК Олимп доступны для всех игроков. Инновационный дизайн и ускоренная обработка данных обеспечивают легкий доступ к широкому ассортименту спортивных событий. Кастомизируйте свой аккаунт с уникальной простотой и навигацией, превращая каждую ставку в волнующее приключение. Скачайте прямо сегодня и начните наслаждаться от ставок на новом уровне с БК Олимп, где каждое событие – это шанс на выигрыш!
Встречайте новинку от БК Олимп для Android, которое полностью преобразит ваш подход к ставкам! С переделанным интерфейсом и ускоренной работой, вы обретете доступ к огромному количеству спортивных мероприятий буквально в несколько касаний. Скачать на андроид букмекерскую Олимп доступны для каждого. Простое управление аккаунтом и понятная навигация сделают процесс ставок наслаждением. Не упустите возможность перейти на новый уровень уже сегодня и разгадайте секреты успешных ставок с БК Олимп, где каждый ваш выбор может привести к победе!